Hide Me Proxy: Complete Guide to Privacy & Security
Online privacy has become a critical concern for businesses and individuals in 2026, with data breaches and tracking technologies more sophisticated than ever. A hide me proxy solution offers a powerful way to maintain anonymity while browsing the web, conducting research, or accessing geo-restricted content. Understanding how these services work and what features matter most can help you make informed decisions about protecting your digital footprint and business operations.
Understanding Hide Me Proxy Technology
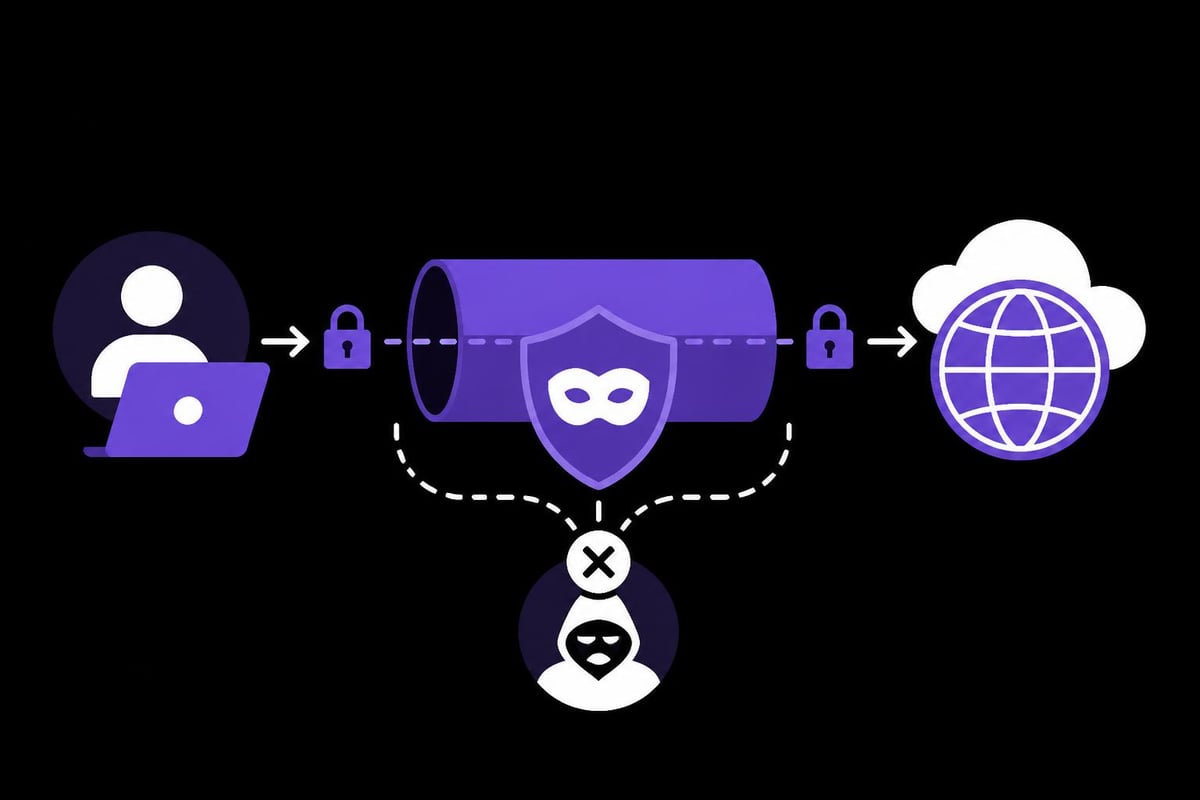
A hide me proxy functions as an intermediary server between your device and the internet. When you route your traffic through this type of proxy, your original IP address becomes hidden from the websites you visit. Instead, they see the IP address of the proxy server, creating a layer of anonymity that protects your identity and location.
The fundamental architecture of proxy servers involves receiving your web requests, forwarding them to destination servers, and then returning the responses back to you. This process happens seamlessly, often without noticeable delays when using high-quality infrastructure.
How Hide Me Proxy Differs from Standard Proxies
Unlike basic proxy solutions, a hide me proxy specifically prioritizes privacy and anonymity. These services typically implement additional security measures:
- Enhanced encryption protocols to protect data in transit
- Strict no-logging policies that prevent activity tracking
- Regular IP rotation to prevent fingerprinting
- DNS leak protection to ensure complete privacy
- Multiple global server locations for geographic flexibility
The distinction matters significantly for businesses engaged in competitive research, market analysis, or data collection. When your competitors can identify your IP address, they may block access or feed you misleading information.
Key Features of Professional Hide Me Proxy Services
Professional proxy services in 2026 offer capabilities that extend far beyond basic IP masking. Understanding these features helps you evaluate whether a hide me proxy solution meets your specific requirements.
Speed and Bandwidth Considerations
Connection speed directly impacts productivity when using proxies for business operations. Modern hide me proxy providers offer:
| Feature | Standard Tier | Premium Tier | Enterprise |
|---|---|---|---|
| Bandwidth | 1-5 Gbps | 5-10 Gbps | 10+ Gbps |
| Latency | 50-100ms | 10-50ms | 1-10ms |
| Concurrent Connections | 5-10 | 50-100 | Unlimited |
| Rotation Speed | Manual | 30s-5min | <1ms |
These specifications matter tremendously for operations like web scraping at scale, where milliseconds can compound into hours of processing time across thousands of requests.
Protocol Support and Compatibility
A comprehensive hide me proxy solution supports both IPv4 and IPv6 protocols. This dual-stack compatibility ensures you can access the entire internet, including newer IPv6-only services and traditional IPv4 websites. Many businesses overlook protocol support until they encounter access issues with specific platforms.
The setup process for proxy servers varies depending on your operating system and use case, but professional services provide configuration guides for all major platforms and applications.
Privacy and Security Advantages
The primary appeal of a hide me proxy lies in its privacy benefits. In an era where data collection has become ubiquitous, maintaining control over your digital footprint provides both competitive and legal advantages.
Zero-Log Policies and Data Protection
Reputable hide me proxy providers implement zero-log policies that prevent the retention of user activity data. This means:
- No browsing history storage
- No connection timestamps
- No bandwidth usage logs
- No DNS query records
- No metadata collection
Research on IP-based authentication mechanisms demonstrates the technical considerations involved in balancing security with privacy. Professional proxy services must implement robust authentication without compromising user anonymity.
Encryption Standards
Modern hide me proxy solutions typically employ:
- TLS/SSL encryption for HTTPS connections
- SOCKS5 protocol support for enhanced flexibility
- Automatic HTTPS enforcement where available
- DNS-over-HTTPS to prevent query interception
Studies exploring location privacy techniques provide insights into how proxy services can implement privacy-preserving technologies that protect user locations while maintaining functionality.
Business Applications and Use Cases
Businesses leverage hide me proxy services for numerous legitimate purposes that require anonymity and geographic flexibility. Understanding these applications helps identify whether this technology aligns with your operational needs.
Competitive Intelligence and Market Research
Companies use hide me proxy solutions to:
- Monitor competitor pricing without detection
- Analyze marketing strategies across different regions
- Track product availability in various markets
- Study localized content variations
- Gather public data without triggering rate limits
The rotating proxies approach proves particularly valuable for these activities, as it prevents target websites from identifying and blocking your research activities.

Content Creation and SEO Operations
Digital marketers and SEO professionals require hide me proxy services for:
- Rank tracking across different locations and devices
- Ad verification to ensure proper campaign delivery
- Keyword research without personalized results bias
- Backlink monitoring at scale
- SERP scraping for competitive analysis
For specialized tasks, SEO-focused proxy solutions offer features tailored to search engine data collection while maintaining compliance with platform terms of service.
E-commerce and Sneaker Botting
The retail automation industry relies heavily on hide me proxy technology. Sneaker enthusiasts and resellers use proxies to:
- Access limited product drops simultaneously from multiple accounts
- Bypass purchase quantity restrictions
- Avoid IP-based bans during high-traffic releases
- Simulate multiple geographic locations for region-specific releases
Specialized mobile proxies for sneaker bots provide residential IP addresses that appear as legitimate customer connections, increasing success rates during competitive releases.
Choosing the Right Hide Me Proxy Provider
The proxy market in 2026 offers numerous options, making selection challenging without clear evaluation criteria. Several factors distinguish professional services from budget alternatives.
Performance Metrics That Matter
When comparing hide me proxy providers, prioritize:
- Uptime guarantees (99.9% or higher for business use)
- Response times under load conditions
- Geographic coverage matching your target regions
- IP pool size for rotation effectiveness
- Success rates for your specific use cases
Reviews like the TechRadar best proxy services guide provide independent assessments of performance across providers, though testing with your specific applications remains essential.
Free vs. Paid Hide Me Proxy Options
While free proxy services exist, they typically come with significant limitations:
| Aspect | Free Proxies | Paid Services |
|---|---|---|
| Speed | Limited | High-speed |
| Reliability | Variable | 99%+ uptime |
| Security | Often minimal | Enterprise-grade |
| Support | Community-based | 24/7 professional |
| Data limits | Heavily restricted | Unlimited options |
The best free proxy options serve casual browsing needs but rarely meet business requirements for reliability and performance. For operations where downtime costs money, paid services provide necessary guarantees.
Browser Extensions and Integration
Many hide me proxy providers offer browser extensions for convenient access. The hide.me Proxy Chrome extension exemplifies this approach, providing one-click proxy activation directly from your browser toolbar.
However, browser extensions have limitations:
- Typically proxy only browser traffic, not system-wide connections
- May lack advanced features like automatic rotation
- Often support fewer server locations than native applications
- Can introduce browser fingerprinting vulnerabilities
For comprehensive protection, especially when using anti-detect browsers for account management, dedicated proxy applications or API integrations prove more effective.
Technical Implementation Strategies
Successfully deploying hide me proxy services requires understanding both technical requirements and best practices for your specific use cases.
Proxy Rotation Techniques
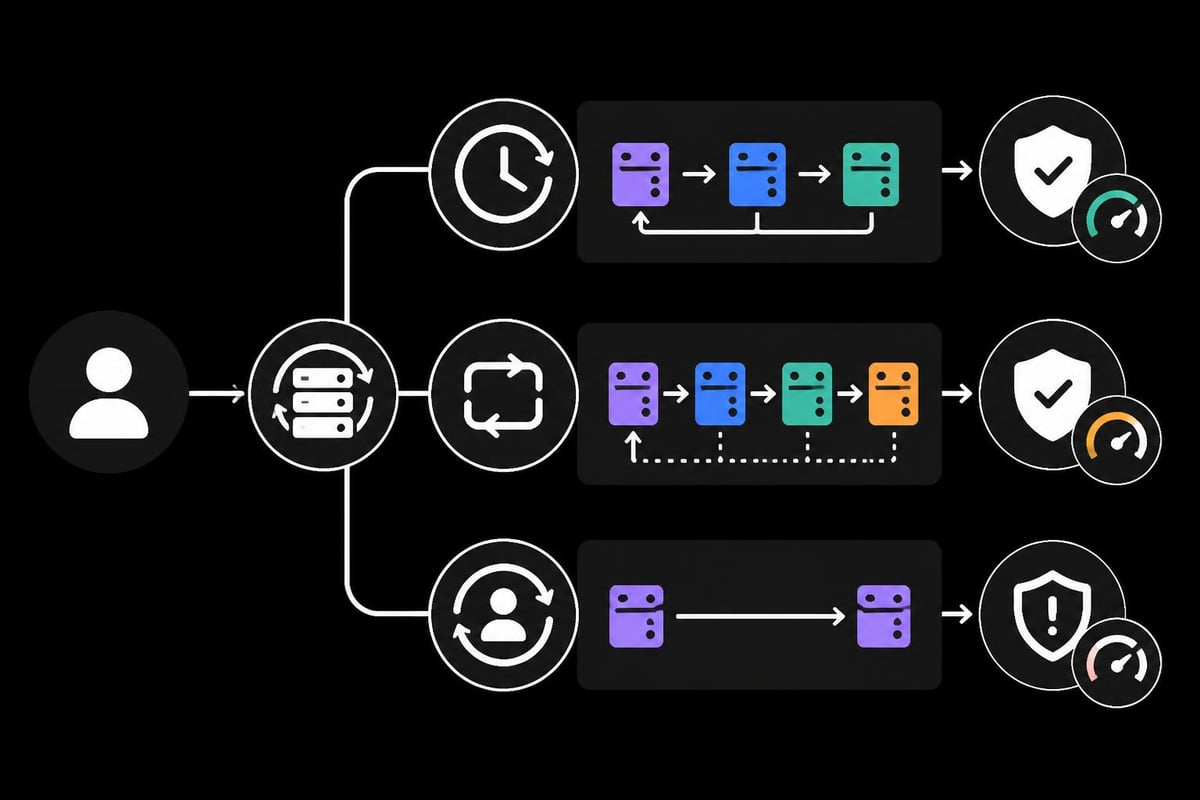
Automatic rotation prevents websites from identifying patterns in your requests. Implementation approaches include:
- Time-based rotation: Change IP addresses at set intervals (30 seconds, 5 minutes, hourly)
- Request-based rotation: New IP for each request or every N requests
- Session-based rotation: Maintain IP for entire user session, rotate between sessions
- Geographic rotation: Cycle through IPs from different regions systematically
Advanced services like those offering 1ms proxy rotation capabilities enable the fastest possible IP changes, crucial for high-volume operations where even minor delays compound significantly.
Authentication and Access Control
Professional hide me proxy services implement multiple authentication methods:
- Username/password combinations for basic access
- API keys for programmatic integration
- IP whitelisting for enhanced security
- Token-based authentication for temporary access grants
Implementing proper access controls protects your proxy resources from unauthorized use while maintaining convenience for legitimate users.
Handling Rate Limits and Bans
Even with a hide me proxy, websites may implement detection mechanisms. Counter these by:
- Randomizing request timing to avoid pattern detection
- Rotating user agents alongside IP addresses
- Implementing realistic session behaviors (mouse movements, scrolling)
- Respecting robots.txt and crawl delays where appropriate
- Distributing requests across multiple IP addresses
The bypass anti-bot detection guide provides detailed strategies for maintaining access to protected resources while minimizing detection risk.
Mobile vs. Datacenter Proxies for Privacy
Understanding the differences between proxy types helps you select the optimal hide me proxy solution for your requirements.
Mobile Proxy Advantages
Mobile proxies route traffic through cellular networks, providing IP addresses assigned to mobile devices. Benefits include:
- Extremely low ban rates due to shared IP usage
- Access to mobile-specific content and APIs
- Superior performance for social media automation
- Natural rotation through carrier IP pools
- Higher trust scores from anti-fraud systems
For platforms like Instagram that aggressively detect automation, specialized mobile proxies provide significantly better results than datacenter alternatives.
Datacenter Proxy Benefits
Datacenter proxies originate from server facilities rather than residential or mobile connections. They offer:
- Superior speed: Direct server connections with minimal latency
- Lower costs: More economical for high-volume operations
- Consistent performance: Predictable speeds and reliability
- Greater availability: Larger IP pools for extensive rotation
- Simpler configuration: Standardized setup processes
For operations prioritizing raw speed over perceived legitimacy, such as large-scale web scraping projects, datacenter proxies often provide the best performance-to-cost ratio.
Hybrid Approaches
Many businesses implement hybrid strategies that leverage both proxy types:
- Use mobile proxies for account creation and authentication
- Switch to datacenter proxies for bulk data collection
- Reserve residential proxies for high-value, detection-sensitive operations
- Implement automatic failover between proxy types based on success rates
This strategy optimizes both costs and effectiveness across different operational phases.
Privacy Laws and Compliance Considerations
Using a hide me proxy involves legal considerations that vary by jurisdiction and use case. Responsible implementation requires understanding these boundaries.
Legitimate Use Cases
Hide me proxy services serve numerous lawful purposes:
- Personal privacy protection during public WiFi usage
- Accessing geo-restricted content you've legitimately purchased
- Conducting security research and vulnerability testing (with authorization)
- Protecting journalists and researchers in restrictive environments
- Business intelligence gathering from publicly available sources
Research on differential privacy for location data demonstrates academic interest in privacy-preserving technologies that align with hide me proxy objectives.
Activities to Avoid
Certain uses violate terms of service or laws:
- Circumventing paywalls without subscription rights
- Engaging in fraudulent transactions or identity theft
- Conducting DDoS attacks or other cyber attacks
- Violating copyright through unauthorized content distribution
- Bypassing access controls on private systems without authorization
Reputable proxy providers include acceptable use policies that prohibit illegal activities while protecting legitimate privacy needs.
Maximizing Performance and Reliability
Getting optimal results from a hide me proxy requires attention to configuration details and monitoring practices.
Configuration Best Practices
Follow these guidelines for reliable operation:
- Test multiple server locations to identify optimal routing paths
- Configure appropriate timeouts to handle slow responses without hanging
- Implement retry logic with exponential backoff for failed requests
- Monitor success rates across different IP addresses and locations
- Cache DNS lookups to reduce unnecessary proxy load
- Use connection pooling to minimize overhead from establishing new connections
These optimizations become critical at scale, where small inefficiencies multiply across thousands or millions of requests.
Monitoring and Troubleshooting
Effective hide me proxy deployments include monitoring for:
- Connection success rates below expected baselines
- Latency spikes indicating network issues
- Geographic routing errors sending traffic through wrong regions
- Authentication failures suggesting credential problems
- Ban patterns across specific IP ranges
Establishing baseline metrics during initial deployment provides comparison points for identifying when performance degrades.
Scaling Considerations
As operations grow, architectural decisions impact performance:
- Load balancing across multiple proxy endpoints prevents bottlenecks
- Regional distribution reduces latency for geographically dispersed operations
- Redundancy planning ensures continuity during provider outages
- Cost optimization through tiered proxy usage based on operation criticality
Services offering unlimited proxy access simplify scaling by eliminating bandwidth concerns, though proper architecture remains essential for performance.
Integration with Business Tools and Workflows
Hide me proxy services integrate with various tools and platforms to enhance functionality and streamline operations.
Development and API Integration
Modern proxy services provide APIs for programmatic control:
Key API functions include:
- Endpoint provisioning and configuration
- Real-time IP rotation control
- Geographic targeting selection
- Session management and persistence
- Usage analytics and reporting
This programmatic access enables automation and integration with existing business systems without manual intervention.
Popular Tool Integrations
Hide me proxy solutions commonly integrate with:
- Selenium and Puppeteer for automated browser testing
- Scrapy and BeautifulSoup for web scraping frameworks
- cURL and Postman for API testing and development
- Browser automation tools for marketing and social media management
- Analytics platforms for data collection and monitoring
Proper residential proxy implementation within these tools requires understanding authentication methods, timeout configurations, and error handling specific to each platform.
Workflow Automation
Businesses automate proxy-dependent workflows through:
- Scheduled rotation during off-peak hours for maximum performance
- Triggered failover when primary proxies encounter issues
- Automatic scaling based on request volume demands
- Geographic optimization routing requests through nearest servers
- Cost management switching proxy types based on budget thresholds
These automations reduce manual intervention while maintaining operational efficiency and cost control.
Privacy protection through proxy services has become essential for modern businesses conducting online research, competitive analysis, and data collection in 2026. Whether you need to mask your IP address for market research, access geo-restricted content, or conduct high-volume web scraping operations, choosing the right hide me proxy solution directly impacts your success and security. PinguProxy delivers enterprise-grade proxy infrastructure with 10Gbps bandwidth, 1ms rotation speeds, and complete IPv4/IPv6 support backed by a strict zero-log policy and 24/7 expert support. Explore how our high-speed datacenter and mobile proxy solutions can enhance your business operations while maintaining complete anonymity.