Unblock It Proxy: Your Guide to Accessing the Open Web
Internet censorship and geo-restrictions have become increasingly sophisticated in 2026, making it harder for users to access the content they need. Whether you're trying to reach blocked websites at work, bypass regional content limitations, or access services unavailable in your country, an unblock it proxy solution provides a pathway to unrestricted internet access. This comprehensive guide explores how proxy technology works, the different types available, and practical strategies for implementing proxy solutions that deliver consistent results.
Understanding How Proxy Servers Unblock Content
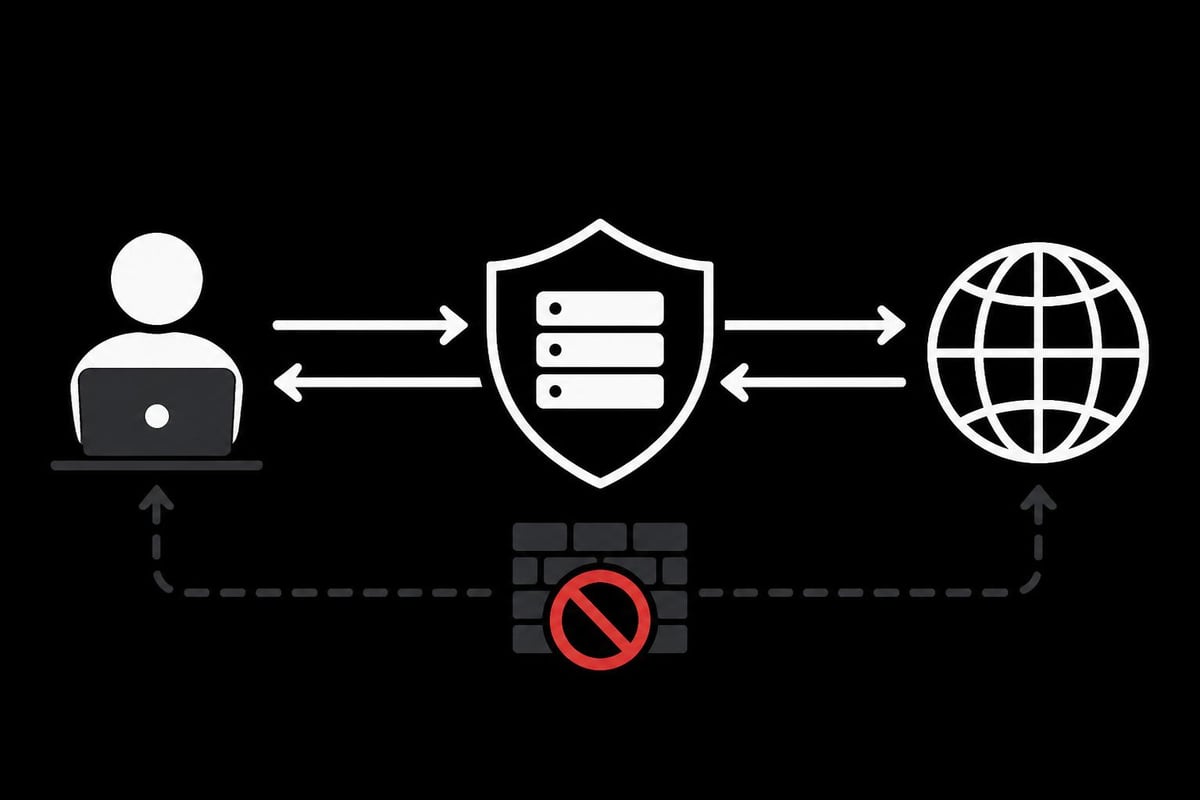
When you need to unblock it proxy technology serves as an intermediary between your device and the internet. Instead of connecting directly to a website, your request routes through a proxy server located elsewhere, effectively masking your real IP address and location.
The process works through several key steps:
- Your device sends a request to the proxy server
- The proxy forwards your request to the target website
- The website responds to the proxy server
- The proxy relays the response back to your device
This routing mechanism allows you to appear as though you're accessing the internet from the proxy server's location rather than your actual position. Geographic restrictions dissolve when the proxy server resides in an allowed region, and network-level blocks become ineffective since the traffic appears to originate from the proxy rather than your device.
Modern proxy solutions have evolved beyond simple traffic forwarding. Advanced implementations incorporate encryption, header manipulation, and protocol obfuscation to avoid detection by sophisticated blocking systems. Research on censorship circumvention effectiveness demonstrates that proxy diversity and rotation significantly improve success rates against adaptive censorship systems.
Different Proxy Types for Different Needs
Not all proxy solutions function identically. The type you choose dramatically impacts performance, anonymity, and reliability.
| Proxy Type | Speed | Anonymity | Best Use Case | Price Range |
|---|---|---|---|---|
| Datacenter | Very High | Moderate | Web scraping, bulk tasks | Low to Medium |
| Residential | High | Very High | Social media, e-commerce | Medium to High |
| Mobile | Medium | Highest | Account management, apps | High |
| SOCKS5 | Variable | High | Gaming, P2P, flexibility | Medium |
Datacenter proxies offer exceptional speed and cost-effectiveness. These proxies operate from data centers rather than residential ISPs, providing stable connections ideal for tasks requiring high bandwidth. However, some advanced detection systems recognize datacenter IP ranges, potentially limiting their effectiveness on certain platforms.
Residential proxies utilize IP addresses assigned to real residential locations by internet service providers. This authenticity makes them significantly harder to detect and block. When you unblock it proxy services using residential IPs, websites perceive your traffic as coming from genuine residential users, dramatically reducing ban rates.
Mobile proxies leverage cellular network connections, providing the highest level of authenticity since they use IPs assigned by mobile carriers. These proxies excel for mobile-specific tasks and platforms with aggressive bot detection. The mobile proxy advantage becomes apparent when managing multiple social media accounts or accessing mobile-exclusive content.
Setting Up Your Unblock It Proxy Solution
Implementing a proxy solution requires careful configuration to ensure both functionality and security. The setup process varies based on your chosen proxy type and intended application.
Browser-Based Configuration
For casual browsing and content access, browser-level proxy settings provide the simplest implementation path. Most modern browsers support proxy configuration through their settings menu:
- Chrome/Edge: Navigate to Settings → System → Open proxy settings → Configure manually
- Firefox: Settings → Network Settings → Manual proxy configuration
- Safari: System Preferences → Network → Advanced → Proxies
When entering proxy details, you'll typically need the proxy server address, port number, and authentication credentials if required. Test your connection after configuration by visiting a IP checker website to verify your apparent location has changed.
System-Wide Proxy Implementation
System-level proxy configuration routes all internet traffic through your proxy server, affecting every application on your device. This approach provides comprehensive coverage but requires more careful management.
Windows users access proxy settings through Settings → Network & Internet → Proxy, while macOS users navigate to System Preferences → Network → Advanced → Proxies. Linux distributions typically manage proxies through environment variables or network manager interfaces.
Important consideration: System-wide proxies affect all applications, including background services and update checkers. Some applications may malfunction if they can't establish direct connections, requiring application-specific bypass rules.

Advanced Proxy Chain Configurations
Power users often implement proxy chains to enhance anonymity and bypass multi-layer restrictions. A proxy chain routes your traffic through multiple proxy servers in sequence, with each server only knowing about its immediate neighbors in the chain.
The configuration might look like:
Your Device → Proxy A (Tokyo) → Proxy B (London) → Proxy C (New York) → Target Website
This multi-hop approach provides several advantages. Enhanced anonymity results from distributed routing, making traffic analysis significantly more difficult. Redundancy ensures that if one proxy fails, the chain can potentially reroute. Geographic flexibility allows you to appear from different locations as your traffic traverses the chain.
Tools like PowerTunnel offer sophisticated proxy chaining capabilities alongside Deep Packet Inspection bypass features, making them valuable for users facing aggressive censorship.
Overcoming Common Proxy Challenges
Even properly configured proxy solutions encounter obstacles. Understanding these challenges and their solutions separates occasional success from consistent reliability.
Dealing with Proxy Detection
Websites employ increasingly sophisticated techniques to identify and block proxy traffic. Common detection methods include:
- IP reputation databases that flag known proxy IP ranges
- WebRTC leaks that expose your real IP address
- Browser fingerprinting that identifies inconsistencies
- DNS leak detection that reveals your actual DNS resolver
Counter these threats through careful proxy selection and configuration. Choose providers with frequently rotated IP pools and strong reputations. Disable WebRTC in your browser or use extensions that prevent WebRTC leaks. Configure your system to use the proxy server's DNS resolvers rather than your ISP's DNS servers.
The anti-bot detection strategies employed by modern websites require equally sophisticated countermeasures. Residential and mobile proxies face significantly less scrutiny than datacenter proxies since their IP addresses appear indistinguishable from regular users.
Performance Optimization Strategies
Proxy connections inherently add latency since your traffic travels through additional servers. Minimizing this performance impact requires strategic choices.
Geographic proximity dramatically affects speed. Select proxy servers physically close to either your location or your target website's servers, depending on your priority. A Los Angeles-based user accessing New York content should ideally use a proxy server on the East Coast rather than routing through Europe.
Connection pooling and persistent connections reduce overhead from repeatedly establishing new proxy connections. When you unblock it proxy solutions support HTTP/2 or keep-alive connections, they maintain open channels that handle multiple requests without reconnection delays.
Bandwidth allocation matters significantly. Premium proxy services like PinguProxy offer 10Gbps bandwidth capacity, ensuring that the proxy connection itself doesn't become a bottleneck even during intensive data transfers.
Advanced Proxy Use Cases
Proxy technology extends far beyond simply accessing blocked websites. Understanding these advanced applications helps you leverage proxies more effectively.
Web Scraping at Scale
Data collection from websites requires proxy rotation to avoid rate limiting and IP bans. When you unblock it proxy services for web scraping, rotating through diverse IP addresses allows you to gather data without triggering anti-bot measures.
Rotation strategies include:
- Time-based rotation (new IP every N seconds)
- Request-based rotation (new IP every N requests)
- Session-based rotation (maintain IP for entire session)
- Failure-triggered rotation (switch IP after errors)
The optimal strategy depends on your target website's anti-scraping measures. Some sites track session continuity and flag rapid IP changes as suspicious, requiring longer session persistence. Others implement strict per-IP rate limits, necessitating frequent rotation. Rotating proxy configurations balance these competing demands through intelligent rotation algorithms.
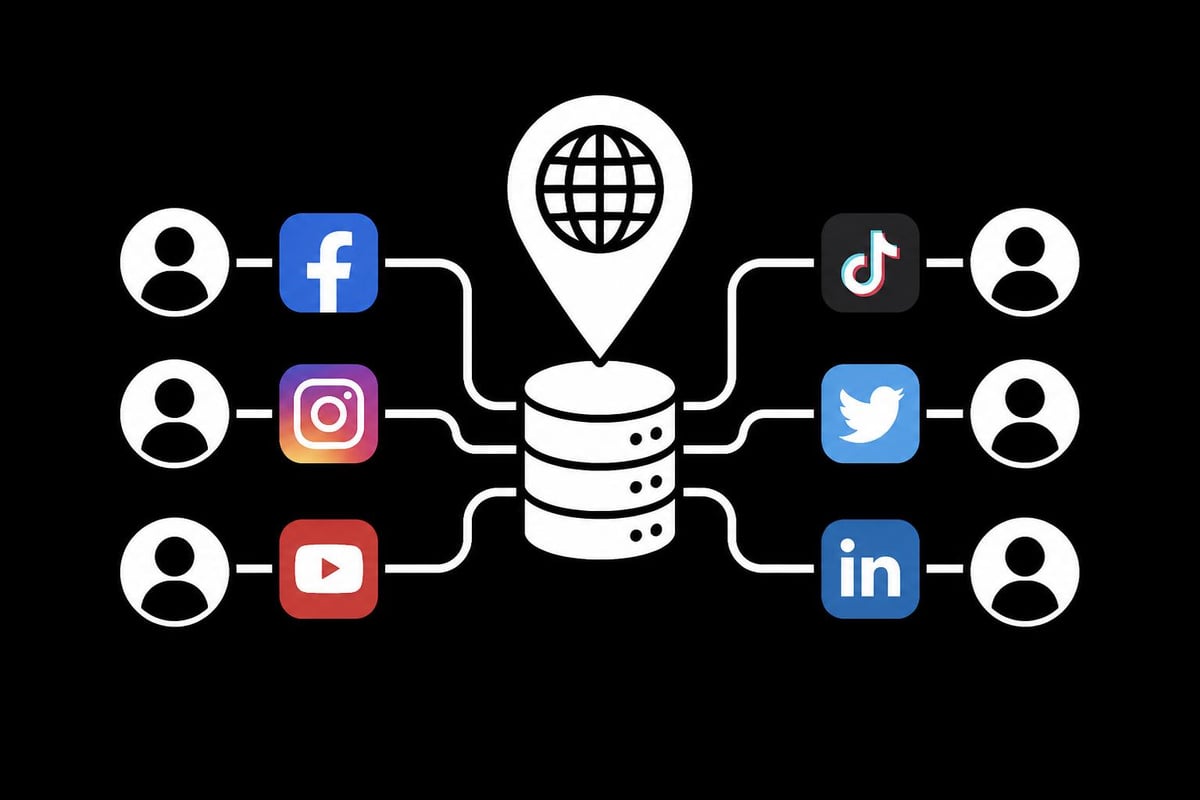
Managing Multiple Accounts
Social media platforms, e-commerce sites, and gaming services typically restrict users to one account. Managing multiple legitimate accounts requires separate IP addresses to avoid association and account linking.
Best practices include:
- Assign each account a dedicated residential or mobile IP
- Maintain consistent IP-to-account pairing
- Use different browser profiles with separate cookies
- Implement realistic timing patterns between account actions
Platforms like Instagram employ sophisticated detection systems that analyze behavioral patterns, device fingerprints, and network characteristics. The mobile proxy advantage for Instagram stems from their authentic carrier IP addresses and dynamic nature, closely mimicking genuine mobile users.
Competitive Intelligence and Market Research
Businesses leverage proxies to monitor competitor pricing, track market trends, and conduct geographic-specific research. Accessing competitor websites from different locations reveals regional pricing variations and localized marketing strategies.
Research applications include:
- Monitoring search engine results from different countries
- Tracking competitor ad campaigns across regions
- Analyzing product availability and pricing by location
- Accessing geo-restricted market data and reports
SEO professionals particularly benefit from location-specific rank tracking, ensuring accurate SERP data reflects how websites appear to users in target markets rather than from the researcher's actual location.
Security Considerations When Using Proxies
While proxies enhance privacy and access, they also introduce security considerations that demand attention. Not all proxy solutions prioritize user security equally.
Free Proxies vs. Premium Services
Free proxy services tempt users with zero-cost access, but these services carry significant risks. Research on free proxy ecosystems reveals concerning findings about reliability and malicious behavior.
Risks of free proxies include:
- Traffic interception and data harvesting
- Malware injection into web traffic
- Credential theft from unencrypted connections
- Unstable connections and frequent downtime
- Advertisement injection into browsing sessions
Premium proxy services address these concerns through encryption, transparent logging policies, and security audits. When you unblock it proxy services from reputable providers, you gain confidence that your traffic remains private and unmodified.
Encryption and Protocol Selection
Not all proxy protocols offer equivalent security. Understanding protocol differences helps you choose appropriately for your security requirements.
| Protocol | Encryption | Speed | Anonymity | Best For |
|---|---|---|---|---|
| HTTP | None | Fast | Low | Non-sensitive browsing |
| HTTPS | SSL/TLS | Fast | Medium | General browsing |
| SOCKS5 | Optional | Medium | High | Flexibility, any protocol |
| Shadowsocks | Yes | Medium | Very High | Censorship circumvention |
HTTP proxies offer no encryption, making them unsuitable for sensitive activities. HTTPS proxies encrypt the connection between you and the proxy server, protecting your credentials and initial request, though the proxy-to-website connection may remain unencrypted.
SOCKS5 proxies support any protocol, not just HTTP traffic, making them versatile for applications beyond web browsing. They can optionally include authentication and work seamlessly with torrent clients, gaming applications, and other specialized software.
Modern circumvention tools like V2Ray combine proxy functionality with advanced obfuscation techniques, making proxy traffic indistinguishable from regular HTTPS traffic even to deep packet inspection systems.
Proxy Rotation Strategies
Static proxies eventually face blocks or rate limits. Rotation introduces fresh IP addresses, maintaining access and preventing detection patterns.
Manual vs. Automatic Rotation
Manual rotation requires user intervention to switch IP addresses. This approach suits scenarios requiring specific geographic locations or when maintaining longer sessions. Users manually trigger rotation through dashboard controls or API calls.
Automatic rotation employs predefined rules or intelligent algorithms to switch IPs without user intervention. Advanced rotation systems analyze response patterns, detecting blocks or rate limits and triggering rotation accordingly.
The most sophisticated rotation implementations use machine learning to predict optimal rotation timing based on historical performance data, request patterns, and target website characteristics. This intelligence maximizes success rates while minimizing unnecessary rotations that could trigger suspicion.
Session Persistence vs. Frequent Rotation
Different tasks require different rotation philosophies. Session persistence maintains the same IP address throughout a logical session, such as completing a multi-step checkout process or maintaining a logged-in state.
Frequent rotation switches IPs aggressively, sometimes with every request. This approach prevents any single IP from accumulating enough request volume to trigger rate limits but requires the target website to tolerate IP changes within sessions.
When you unblock it proxy rotation carefully balances these approaches based on your specific requirements. Web scraping best practices recommend matching rotation frequency to target site strictness, starting conservative and increasing rotation speed only as needed.
Proxy Authentication Methods
Securing proxy access prevents unauthorized usage and potential abuse. Understanding authentication options helps you implement appropriate access controls.
IP Whitelisting
IP whitelisting restricts proxy access to specific source IP addresses. Only requests originating from approved IPs can use the proxy service, providing strong security when users have static IP addresses.
Advantages:
- No credential transmission (nothing to intercept)
- Simple implementation
- Fast authentication (no credential verification delay)
Limitations:
- Requires static IP addresses
- Difficult for mobile users
- Complicated for dynamic IP environments
Username/Password Authentication
Credential-based authentication allows access from any location using valid username and password combinations. This flexibility suits users with dynamic IPs or those accessing from multiple locations.
Implementation typically embeds credentials directly in proxy URLs: http://username:[email protected]:port. While convenient, this approach exposes credentials in application logs and browser history unless handled carefully.
Token-Based and API Key Authentication
Modern proxy services increasingly implement token-based authentication, providing enhanced security through time-limited or single-use tokens. API keys enable programmatic access for automated scripts and applications.
Benefits include:
- Granular access control and permissions
- Easy revocation without changing primary credentials
- Usage tracking per token or key
- Integration with automated workflows
Token systems allow different tokens for different applications, limiting exposure if credentials leak. When one token becomes compromised, you revoke only that token rather than changing your entire account password.
Regional Considerations and Compliance
Proxy usage intersects with various legal and regulatory frameworks depending on your location and intended use. Navigating these considerations ensures compliant and ethical proxy deployment.
Geographic Restrictions and Licensing
Content licensing agreements often restrict availability by region. Streaming services, for instance, negotiate separate licensing deals for different countries, creating geographic availability variations. While proxies technically enable access to geo-restricted content, doing so may violate service terms.
Corporate environments face different considerations. Businesses using proxies for competitive intelligence, market research, or data collection must ensure compliance with:
- Website terms of service
- Data protection regulations (GDPR, CCPA)
- Industry-specific compliance requirements
- Export control regulations for certain data types
Countries facing heavy censorship present unique challenges. Recent reporting on Iranian circumvention efforts demonstrates how citizens combine multiple technologies, including proxies, to maintain internet access despite government restrictions.
Ethical Proxy Usage
Responsible proxy usage respects both legal requirements and ethical considerations. When you unblock it proxy technology for legitimate purposes, you contribute to an open internet while avoiding harm to service providers.
Ethical guidelines:
- Respect robots.txt and crawl-delay directives
- Implement reasonable rate limiting
- Identify your bot with accurate user agents
- Avoid accessing clearly prohibited content
- Honor website terms of service where possible
Balancing access needs with responsible usage maintains a sustainable proxy ecosystem. Excessive, aggressive scraping harms target websites through increased infrastructure costs and degraded performance for legitimate users.
Monitoring and Maintaining Proxy Performance
Successful proxy deployment requires ongoing monitoring and optimization. Performance degrades over time as IP addresses accumulate reputation issues or network conditions change.
Key Performance Metrics
Track these essential metrics to maintain optimal proxy performance:
- Success rate: Percentage of requests successfully completed
- Response time: Average latency from request to response
- Throughput: Data volume transferred per time unit
- Error rate: Failed requests by error type
- IP reputation: Blocklist appearances and trust scores
Establishing baseline performance metrics enables quick identification of degradation. Sudden success rate drops or latency spikes indicate problems requiring investigation.
Troubleshooting Common Issues
When proxy performance declines, systematic troubleshooting identifies root causes:
Connection timeouts often stem from overloaded proxy servers or network congestion. Testing alternative proxies isolates whether the issue affects specific servers or your entire proxy pool. Geographic proximity testing determines if routing distance contributes to delays.
Authentication failures typically result from expired credentials, IP whitelist misconfigurations, or account issues. Verify credentials remain valid and check that your current IP address appears on whitelists if using IP authentication.
Blocked requests suggest IP reputation problems or detection by target websites. Rotating to fresh IPs often resolves immediate blocks, while persistent blocking indicates more sophisticated detection requiring residential or mobile proxies.
The residential proxy advantage becomes clear when datacenter IPs face consistent blocks despite rotation, necessitating migration to more authentic IP sources.
Future Trends in Proxy Technology
Proxy technology continues evolving in response to increasingly sophisticated blocking mechanisms and expanding use cases. Understanding emerging trends helps future-proof your proxy strategy.
AI-Powered Proxy Management
Machine learning algorithms increasingly optimize proxy selection, rotation timing, and request patterns. These systems analyze historical performance data, learn target website behaviors, and adapt strategies in real-time.
AI applications include:
- Predicting optimal rotation timing before blocks occur
- Automatically adjusting request rates to avoid detection
- Selecting ideal proxies based on task requirements
- Detecting and responding to anti-bot measure changes
Decentralized Proxy Networks
Blockchain and distributed ledger technologies enable new proxy architectures where users share bandwidth in peer-to-peer networks. These decentralized systems eliminate central control points, making them resilient against shutdown attempts.
Research into censorship-resistant infrastructure demonstrates novel approaches like IPNS-based DNS over HTTPS that create moving-target services difficult for censors to block permanently.
Protocol Obfuscation Advances
As deep packet inspection becomes more sophisticated, proxy protocols incorporate advanced obfuscation techniques. Traffic disguised as common protocols like HTTPS avoids detection even when censors analyze packet contents and timing patterns.
The delay between proxy discovery and blocking provides a critical window for circumvention. Ephemeral proxies that exist briefly before rotation exploit this delay, staying ahead of blocking mechanisms through constant renewal.
Choosing the right proxy solution depends on balancing your specific access requirements with security, performance, and budget considerations. Whether you're bypassing simple network restrictions, conducting large-scale web scraping, or managing multiple accounts across platforms, understanding proxy fundamentals ensures successful implementation. PinguProxy delivers the high-speed datacenter and mobile proxies with IPv4/IPv6 support, zero-log privacy, and 1ms rotation you need to maintain reliable access to the open internet in 2026.